My various illnesses keep me in bed a lot of the time. Not only that, but quite often I don’t have much choice about what position my body goes in. At my better times I can sit up in bed with my laptop or book on my lap. If slightly worse then I put my laptop on the shelf next to the bed and lie sideways to use it, but that can quickly lead to pain. If I am really exhausted then I quite often lie on my front with my phone on the bed next to my head and one hand on the phone to type with, however this still causes pain in my arm, hand and shoulder and sometimes my lower back too. At my worst points the only near-comfortable position is completely flat on my back with my arms on the bed by my sides. This obviously makes it difficult to read a book, or use a laptop computer, or even just use my smartphone.
I do have other options for entertainment at these times - I could use the radio or an MP3 player to listen to music or audio books. However I use my computer extensively to keep in touch with friends (and chat to people to minimise my depression) and to write on my blog. If I have any chance of paid work in the future it is likely to be writing or programming with the aid of my computer and so being able to use it more in bed is quite important.

Ultra 510i
I’ve been thinking about solutions to this problem. The logical solution to me would be to mount a computer monitor over the bed on an arm attached to the wall. This isn’t exactly easy since there is a shelf unit between the bed and the wall to the side of me which is quite a big gap to bridge. I could attach an arm to the wall behind the bed but again it has to extend quite a long way. In addition I want the monitor to be able to swivel for viewing above me or in front of me. There don’t seem to be many arms that fit the specification, although I have found two from ErgoMounts that might work. The Ultra 510i Long Reach Inverted Wall Mount LCD Arm (Pictured to the right) costs £411 while the Wall Mount VisionPro 500 Series Long Reach Gas Assisted LCD Arm (Shown below) costs £215 but is not quite long enough to be comfortable. With this solution I would have a computer of some sort next to the bed, and a wireless keyboard and mouse on my lap.

VisionPro 500
Such a system might work, but is quite expensive and limited so what are the other options?
Duncan from Trabasack suggests that I could use a Trabasack Mini lap tray/bag to suspend a netbook computer from. The Connect version has a velcro front and points to attach straps, so I could attach the netbook to the Trabasack with velcro and use the straps to hang it from a simple arm attached to the wall which should be cheaper than an articulated arm. The downside of this is that I would have only the small screen of my eeePC 900 and it isn’t very powerful either, but I can use it to get remote control of the PC on my desk which would do all the work. Duncan has sent me a Trabasack to try, so I’ll report back on how that goes.

Another option which has caught my attention is virtual reality goggles. Basically glasses with screens inside, the best available are made by Vuzix. There is a whole range of Vuzix iWear. The Wrap 280 widescreen is the bottom of the range, but it has a resolution of 384×240 (That’s how many dots fit on the screen) which makes it useless for text-based computer work and barely usable for watching video. It is, however, available for £99 or even cheaper refurbished. The top of the range Wrap 1200 has an almost-acceptable resolution of 848×480 (still pretty low) but costs £399. The Wrap 920 looks like it might be worth a try though. It has a resolution of 640×480 which is what computers displayed about 18 years ago but is only slightly lower than what my smartphone displays so it might be usable. The 920 is £199 but is also available refurbished for £129. All three of these options would need a £40 adapter to plug in to the VGA output of a computer. I could use one of these displays in any position in bed, but whether I can use them for writing a blog post or chatting to people remains to be seen.

Then there is the question of keyboard and mouse. While it is straightforward to use a mouse on the bed, even with my eyes covered with display screens, a full size keyboard isn’t ideal. I can touchtype but I still have to keep my hands up on the keyboard on my lap rather than down by my sides where they are more comfortable. To solve this problem I have been looking at Chorded Keyboards. These devices use only a few buttons to type the whole alphabet by pressing combinations of keys at the same time. The original Microwriter would have been useful here but two modern versions I am considering are the CyKey and the Twiddler 2.
The CyKey (shown below) has nine keys instead of six but works with combinations of keys in a similar way to the Microwriter. It costs £74. It should work alright when placed under my hand on a bed and allow me to type without moving my hand around. Unfortunately I will still have to move my hand to use the mouse.

Twiddler 2
The Twiddler 2 (pictured on the right) has a few more keys than the Microwriter or the CyKey but the principle is the same. It has a thumb-operated pointer stick too so that it can replace both keyboard and mouse. The Twiddler is popular with designers of wearable computers because it can be used without sitting down and using a table. It is more expensive than the CyKey at $199 plus postage from the USA but looks to be the best option if I can find the money.
I am also planning to use a Raspberry Pi as my bedroom computer. The Raspberry Pi is a new tiny cheap computer intended for use primarily to encourage children to learn computer programming but it looks to have many other uses. It costs about £29 for the top model and runs Linux. I intend to use it as a Thin Client, to connect to my PC via Remote Desktop, meaning that it will show me what is on my PC in a different room, and my keyboard and mouse in front of me will control that PC.
All of this portable technology has given me some interesting thoughts. I could team up a Raspberry Pi with a Vuzix Wrap 920 display and a Twiddler 2 chorded keyboard. Add in my USB powerpack and a WiFi/Bluetooth adapter to connect to the internet, and I will have a complete wearable computer for use anywhere. I quite like that idea if I can possibly find the money. Now, about my early birthday presents…
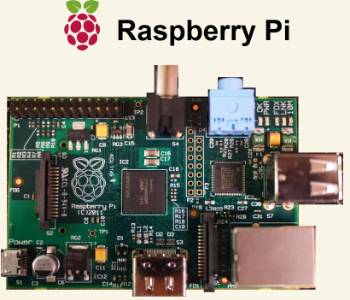
So new it hasn't got a case yet