Let me preface this by saying that contact from friends through Twitter when I have been at low points has absolutely saved my life. I would be dead if it were not for my friends on Twitter. Now, with that out of the way, read on.
The Samaritans have proudly launched a new app that when activated will alert the user to tweets from people they follow that might betray suicidal thoughts. When you sign up to Samaritans Radar it will watch the tweets of everyone that you follow and will email you as soon as it notices any tweets with key words and phrases related to depression. It is described as working through “a specially designed algorithm that looks for specific keywords and phrases within a Tweet.”
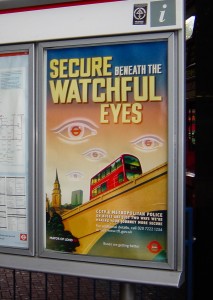
Spotting when a friend is low or suicidal is a laudable aim but this app immediately rings huge alarm bells for me. There are huge implications for privacy and consent. It seems that the Samaritans have considered only the privacy of the person that signs up to use the app, but says nothing about the privacy or consent of the people that the app monitors. In fact the website assures us that “The people you follow won’t know you’ve signed up to it and all alerts will be sent directly to your email address.”
The reaction to this app has been divided. On the one hand there are scores of people who seem very pleased with this and think it is a useful tool and a great idea. On the other hand, nearly everyone who I know who has or has had mental health problems has been immediately shocked, outraged and scared by it. The objections are many, including that people may self-censor if they think that they will trigger this app, that they may trigger it too often, that the app may be used by stalkers to pinpoint when a person is most vulnerable. Or spammers. Or evangelists. It is natural, then, to ask whether someone can reject Radar. Alas, it seems not. The Samaritans director of policy was asked the question and his response was troublesome to say the least: lock your Twitter account.
https://twitter.com/Ferns_Joe/status/527450160214056960
The idea that people should lock their account to avoid something is one that is also frequently used to defend harassment and to defend doing nothing about harassment. It always comes from people who have not experienced the issues that might drive a person to hide in that way and who thinks it acceptable to tell marginalised people to hide themselves if they don’t like society. It is unacceptable to drive people to hide rather than address a problem within society. The same viewpoint says that tweets are public and searchable therefore anything that people chose to do with them is OK. That is also unacceptable.
https://twitter.com/Ferns_Joe/status/527452663185948674
Radar may be limited only to those who follow me but I have over 6,000 followers. I follow only half that number, and I actually, really know only a few hundred at most. Among my followers are people who hate me and people who are my political enemies who are keeping tabs on my activities so limiting something to my followers is not good enough.
https://twitter.com/PaulAshYoung/status/527461305104744448
https://twitter.com/Ferns_Joe/status/527454616024539137
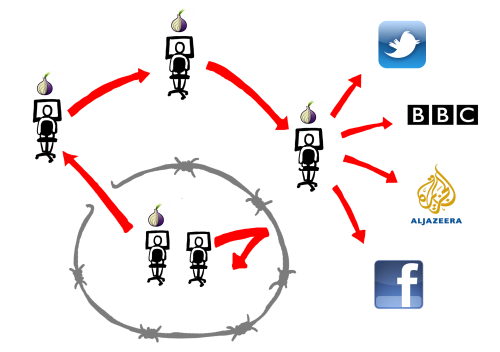
The suggestion that we don’t know how Twitter works is really insulting. People use Twitter in many different ways. For some Twitter is a news stream, for others it is a marketing channel. It is a place to chat with friends, a place to campaign politically, a place to turn for help, a place to commiserate. Twitter is just a place that humans inhabit and do human things in. The trouble is, Twitter doesn’t know this. The terms and conditions allow the whole stream of tweets to be sold to organisations for various purposes with or without consent.
Here’s the thing. We do know that tweeting is broadcasting. But tweeting is also a conversation among friends in a pub that can sometimes be overheard by others. Some of those others may be casual acquaintances, complete strangers, investigators from the DWP, or journalists. We may or may not care if they overhear. Sometimes something said to friends in a public place can be reported in the news worldwide. That doesn’t mean it’s what you expect to happen. Neither do we expect a mental health charity to create a tool that makes it easier to violate people’s boundaries.
Are you the kind of person that sneaks up to people’s private conversations to monitor them just because they’re in a public place? Because that doesn’t tell me I don’t know how things work, that tells me that you don’t know how society works. There’s an awful lot of people who have no idea of boundaries and think lack of technical block is society’s blessing to do something.
https://twitter.com/geeoharee/status/527461872589484033
https://twitter.com/IamMrJ/status/527459149068902401
The thing is, Samaritans almost get how Twitter can be used. On the Radar web page they say:
“Samaritans recognises that social media is increasingly being used as an outlet for people to share their feelings. In addition, there are some who may go online in the hope that someone will reach out and offer support.”
They must realise that the way a person sharing their feelings uses Twitter is different to the way that marketers or organisations use Twitter.
I think that the concept of an app that can alert a trusted friend about bad mental health episodes could have some merit however any such app must obtain full consent from the person being monitored and it must allow the individual to choose who they trust enough to receive the alerts. I might even use such an app in those circumstances.
Try again, Samaritans.
Please sign the petition to get Samaritans Radar shut down
Related Reading
Former Samaritans volunteer @elphiemcdork: The Samaritans Radar app – the problem is right there in the name.
@YetAnotherLefty: On “Samaritans Radar”
@adrianshort: Samaritans Radar: paved with good intentions
Serious questions raised over whether Radar is compliant with the Data Protection Act:
@bainesy1969: Samaritans Radar – serious privacy concerns raised
@aimscetera: Email to Samaritans about Radar
@susanhalluk: Weary, Stale, Flat, Unprofitable - and in breach of the Data Protection Act
You can reach The Samaritans on 08457 90 90 90.