I wrote a few weeks ago on the importance of secrecy. I also reviewed a book by Cory Doctorow, Little Brother. One of the things that caught my eye while reading the book was a version of Linux with an interesting description.
“Paranoid Linux is an operating system that assumes that its operator is under assault from the government (it was intended for use by Chinese and Syrian dissidents), and it does everything it can to keep your communications and documents a secret.”
Cory Doctorow (Little Brother, 2008)
In the story, activists had put together an alternative operating system based on Linux and called Paranoid Linux. An operating system is the software that tells the computer how to behave, where to store information, and determines what software or ‘Apps’ you can use. Paranoid Linux took the form of a Live CD, that is a CD that can be used to startup a computer and work without storing anything on the built in disk. The interesting thing about Doctorow’s description of Paranoid Linux is that it brings together a number of technologies that when combined make a persons activities on the computer and on the internet completely anonymous, untraceable and unreadable to anyone not intended to see them, and yet completely trustworthy and verifiable as the person they claim to be to the intended recipient. The technology described also allows a person to turn on their computer in any reasonably populated location and be connected to the internet wirelessly by hopping through other computers in a mesh network to find an internet connection.
Another facet of the story is that Xboxes were given away for free in order to sell software. (The razor blade model) The availability of free computers is a powerful temptation, and so crackers had broken the security that allowed the Xbox to only play official games, and produced a version of Paranoid Linux that allowed the free Xboxes to be used as full computers. Through a combination of freely available hardware and underground distribution of CDs containing Paranoid Linux, it because ubiquitous and allowed people in close enough proximity to form a mesh network.
The amazing thing about the technology described is that it all exists. The frustrating thing is that no one has managed to bring it all together in the way described in the story. An attempt at modeling some of it had been started with a real world Paranoid Linux project, but that has since ceased development and no one else has taken up the challenge.
So what are the technologies involved?
- Mesh networking
- Random anonymous routing
- End-to-end encryption of all traffic such as web pages, email, chat and voice
- Digital signatures and proof of identity
- Fake internet traffic (Chaff) to provide a decoy and hide real information
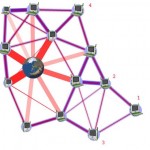
Mesh networking is a way of linking up computers in an ad-hoc way so that a computer at one side of the group could send a message via computers in the middle all the way to the other side. Since all computers in a mesh network are linked, if one has a connection to the internet then all of them can use it. Mesh networks provide a way for people to get on line in rural areas with few internet connections, and has been implemented by the One Laptop Per Child ($100 laptop) project for use in third world countries. Mesh networks are not yet popular, but if they became so then they could be used to extend any free public WiFi points far beyond their current reach.
 Random anonymous routing has been implemented in the Tor project. With Tor installed on a computer, web pages and other communications are bounced through computers belonging to several other Tor users, picked at random, before reaching the desired server. Tor is in popular usage right now in places like China and Iran to allow ordinary people to get around censorship imposed by the government. Tor is recommended by organisations like indymedia and the Electronic Frontier Foundation as a way to safeguard the privacy of their members. Tor is also recommended for whistle blowers to use when communicating with journalists. Even governments use Tor. From the Tor website:
Random anonymous routing has been implemented in the Tor project. With Tor installed on a computer, web pages and other communications are bounced through computers belonging to several other Tor users, picked at random, before reaching the desired server. Tor is in popular usage right now in places like China and Iran to allow ordinary people to get around censorship imposed by the government. Tor is recommended by organisations like indymedia and the Electronic Frontier Foundation as a way to safeguard the privacy of their members. Tor is also recommended for whistle blowers to use when communicating with journalists. Even governments use Tor. From the Tor website:
“A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.”
 Encryption is already used on web pages for activities such as shopping and sometimes when logging in to a website. (The padlock symbol that we are all trained to look for means that encryption is in use between the web browser and the server.) Encryption can be added to other communications such as email using software like Pretty Good Privacy (PGP) or the free open source equivalent Gnu Privacy Guard. (GnuPG)
Encryption is already used on web pages for activities such as shopping and sometimes when logging in to a website. (The padlock symbol that we are all trained to look for means that encryption is in use between the web browser and the server.) Encryption can be added to other communications such as email using software like Pretty Good Privacy (PGP) or the free open source equivalent Gnu Privacy Guard. (GnuPG)
Both PGP and GnuPG use what is called Public Key Encryption where every user has a public and a private key. Anything encrypted with the public key can only be read using the private key, which means that it is possible to send information securely without having to exchange keys in secret. Conversely, anything can be signed with the private key, and anyone that has the public key and trusts that it is the right one, can be certain that the person that signed that document is who they say they are and also that the document has not been modified since then.
I could not find any software that provides fake internet traffic (Chaff) to cover up the real communications. People have talked about it but few have bothered to create any tools to do it. Perhaps this one is not so necessary.
Another technology that I would want to add to the mix is an Intrusion Detection System that looks out for malicious attacks on the computer via the internet and watches operating system files to make sure that they are not modified by malicious software or by outside agencies attempting to spy. This software should provide a warning if a system is compromised.
So why do we need all of this privacy? The tools that I have described here are already in use all around the world. Most often they are used to hide from oppressive governments in places such as China and Iran, but they are useful for many other people. Journalists, whistle blowers, activists, celebrities avoiding publication of their information, people working in sensitive jobs, and many others can all make use of these privacy tools. Everyone has sensitive information, many transmit that over the internet. Privacy tools can be used in any location to help secure information. For example they would be useful when using open public WiFi which are otherwise easily subverted to spy on the end users.
There is a possibility that using tools to allow anonymity and privacy could draw attention to the people using them. If only a few use such tools then it could be possible to identify the internet connections with obfuscated traffic and therefore find their addresses. The answer lies in making sure that there are legitimate uses of these tools and persuading as many people as possible to use them. When all internet traffic is secured then nothing will stand out from the crowd to be tracked.
Would this get in the way of police investigations? Undoubtedly the answer is yes. Routine encryption and obfuscation of internet traffic will prevent the police from keeping tabs on suspects. And I have sympathy for them. The ability to read the email of a bomber before he does damage is very helpful in investigations, just as is the ability to tap their phone. But realising that this will make it harder for police investigations does not cause me to change my mind about it. The police and the myriad of government agencies have been routinely trawling the commmunications of many people. That is not seen as a problem when it leads to an arrest before a bombing or a kidnapping, but people should have a different opinion when the ones being observed are not planning any crime, but simply to oppose the government on illiberal laws or cuts to services, or support the publication of information. Those in power are not meant to go on fishing expeditions for our data, they are supposed to obtain a warrant from a judge on those occasions when a suspects communications could provide evidence to prevent a crime or to prosecute.
A would love to have a new edition of Paranoid Linux which bundled all of these privacy tools and made them easy to use straight out of the box. Perhaps it could be built as an offshoot of one of the existing distributions of Linux such as Ubuntu, which already has the ease of use that would be required. I see no reason why these tools could not be distributed as one installable package that could be added to an existing operating system. There could even be a version for Windows. The key thing is to make the tools available to all, easy to configure and use, and above all to make people aware of their existence and the reasons to use them.
Addendum: The non-technical summary
What I want is a system that can be used to start a computer that will automatically connect to the internet through random nearby computers, will encrypt everything that is sent over the internet, will send said information on a random untraceable route through the internet, and produces emails and documents that are provably written by a certain person and not tampered with.

Regarding the “availability” of an operating system that is more secure I have found that “Ubuntu” has bee the most secure for me, For example the number of open ports on a default installation of windows = many, the same default install on Linux Ubuntu would leave no ports open and this I could see as being “Parinoid Linux”.
I may be these days pro Ubuntu for security but the fact is if some one does want your information from you machine they will be able to get it in some way or form. If one technology is there to secure data there will be a way of un-securing data.
I think that people should think about what they are going to send over a network before sending it. Especially now the “networked society” is becoming an ever increasing “cloud” of connectivity. And a privacy attack could in theory come from any place on that “cloud”.
Good article btw
If the Live CD option takes too long to boot, you can use Truecrypt (http://www.truecrypt.org/) to make encrypted storage or even encrypt existing partitions. It comes with an excellent idea of hidden partitions that gives you dual passwords and thus plausible deniability in countries where you can be legally forged to hand over passwords or face jail.
In these days where even copies of ‘cookbooks’ that we used to hand round our playground on floppy disks could now land you in jail on terrorism charges, encrypted storage is a vital tool for anyone who values freedom of information.
Two alternatives to Tor you could also consider for encrypted communications are I2P and JAP.
These services are also useful should you need to poke holes through an overly-restrictive corporate firewall. They are portable so there’s no need to have permissions to install anything.
forged = forced
I hadn’t looked at alternatives. I will read up on I2P and JAP.
Old post, I know but just a few quick notes because I hadn’t seen it before.
Someone attempted to implement the idea of “chaff” in a tool called Haystack but it turned out to be horribly flawed: see http://www.guardian.co.uk/technology/2010/sep/17/haystack-software-security-concerns
Truecrypt has a number of serious questions about it not least about who is funding it. The binaries do not match what you can build from the source and it has not been independently audited by security professionals for this reason. If you want crypto on linux use dm-crypt / LUKS.Bear in mind, however, that you can be sent to jail in the UK for refusing to hand over your password on request from the police.