A common feature of oppressive regimes is control of information. In Egypt recently the government not only blocked television signals from the likes of Al Jazeera, but they actually resorted to almost completely shutting down the internet across the whole country in an effort to prevent protesters from organising. In China, Iran, Syria, Cuba, Yemen, Saudi Arabia, and many other places, the governments block access to sites that they consider a threat to either the government or to the moral values of the people. This usually includes social networks like Facebook and Twitter and news organisations like the BBC and Al Jazeera.
The solution
While a partial connection to the outside world is available, there is a way to get full access - with the Tor project which you can find at www.torproject.org. Tor makes use of a network of volunteers across the world to smuggle information across the borders. The Tor website describes it like this:
“Tor protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world: it prevents somebody watching your Internet connection from learning what sites you visit, and it prevents the sites you visit from learning your physical location.”
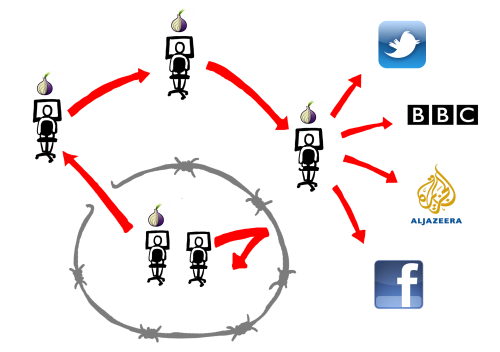
Any person in any country can run Tor software on their own computer. When someone in, say, Iran wants to get access to Facebook, Tor sends their request to someones personal computer in the UK or USA, which passes it on to Facebook or perhaps through another couple of computers first. The authorities in Iran will see only a connection between two personal computers and they will not know what web site is accessed, if they notice anything at all. Tor is aimed mostly at web browsing and instant messages as there is not enough bandwidth to allow file sharing and video streaming.
Tor relies on volunteers in “safe” countries to run their software in order to give access to the people in oppressed countries. This is where you can help. It doesn’t take long to download the software, and following the guide you can be helping people get access to subversive information in no time.
What are the drawbacks?
Tor can be used by anyone, to transfer any information. There is no guarantee that people you don’t like will not use Tor. If you run Tor on your own computer, it is likely that information that you disagree with will pass through your computer. This could be of any nature, including information helpful to terrorists, pornography, or other distasteful matters, and it is possible it could be appear to come from your computer, although it will only ever exist in passing and will never show on your computer later. It could have the same legal consequence as allowing others to use your WiFi. This is a drawback, but if we are to ensure freedom of speech then it is something that must be dealt with in ways other than by blocking their connections. In the end this is an ethical question which you must make up your own mind on.
Tor uses some of your bandwidth. If you have a download limit, Tor could use up that limit quite easily. It can also be inconvenient if Tor is using too much of your connection when you want to use it. You can limit the speed (bandwidth) used by Tor so that it does not intrude on your usage, but you cannot set a download limit other than by turning off the relay yourself if too much is downloaded.
It is not illegal to run Tor in most places outside of those oppressed countries. It might, however, break rules set by your employer, internet provider or parents if you use their connection. This may or may not be a reason to change your mind on running Tor, or you might be running Tor to break through restrictions set by those people.
Some people think it is possible that there might be a “backdoor” in the software that would allow US government agencies to track down users of Tor. Tor was originally created for the US Naval Research Laboratory before being sponsored by the Electronic Frontier Foundation, and then becoming an independent non-profit organisation. Tor is open source, that is, anyone can look at the code behind the software to check for things that shouldn’t be there. I personally think it unlikely that there is a backdoor. The Tor project have this to say about it:
“There is absolutely no backdoor in Tor. Nobody has asked us to put one in, and we know some smart lawyers who say that it’s unlikely that anybody will try to make us add one in our jurisdiction (U.S.). If they do ask us, we will fight them, and (the lawyers say) probably win.”
What about elsewhere?
Tor is not just useful in countries known for oppression, but could also be useful in other places. Australia wants to censor connections against a list of bad websites. In the USA the president is talking about getting an “Internet off switch.” If that is implemented badly, then Tor may get around it. The UK already censors connections through the Internet Watch Foundation. (IWF) Our government want to filter all connections for pornography by default, and is even now attempting to keep records of of all our communications. Not the contents of them, but a record of every phone call made, every email sent, every web page looked at. Using Tor to help those in other countries can have the added advantage of erasing your own records should the government ever decide to take an interest in you.
Useful information
How to install Tor by Latentexistence
How to setup a Tor relay or Tor bridge by AnonyGreen
Measuring Tor and Iran Some information about how much Tor is used in Iran.
Countries that censor the Internet


I really wish I could use Tor in China, but nobody I know has ever got it to work. The government have some way of blocking all Tor-like connections.
It is possible to tweak some settings in Tor and set up a direct connection (a bridge) between someone behind the firewall and a volunteer in a more open country. This method is on a different port and looks different to the authorities and so is harder to block. The second link that posted at the end of the article has some posts by people that are doing that for Iranians. I can set up a bridge so that you can test this if you want.
I might give it a go soon, not enough spare time for tinkering ATM (wife’s about to have our baby), but I’ll give it a go in the next few weeks.
All proxies are blocked here. Some VPNs are good, but generally you have to pay. The best solutions I’ve found so far are Hotspot Shield and Ultrasurf, but the popup ads and connection speed are a bit annoying. And I can’t upload to youtube for some reason.
The media in the UK generally assume the great firewall is just an anti-democratic measure, but I’m certain that economic protectionism is if anything an equal cause. Might write something about it myself, see if I can get livejournal blocked again.
Tinkering is minimal. Opening a port or two in your local firewall aside, you can use Vidalia to configure Tor and have a fully functional relay or exit node running in about sixty seconds.
As for VPNs, have you looked into airvpn.org?
“If you run Tor on your own computer, it is likely that information that you disagree with will pass through your computer. This could be of any nature, including information helpful to terrorists, pornography, or other distasteful matters, …”
Don’t scare people like this.
This is only true for a computer on which you create a relay, an exit node or a hidden service.
Simply using a Tor client does not do this.
“Simply using a Tor client does not do this.”
Did you read the article? I’m talking about running a Tor Relay.